Filter by
Edible Medicinal and Non-Medicinal Plants
This book covers such plants with edible modified storage subterranean stems (corms, rhizomes, stem tubers) and unmodified subterranean stem stolons, above ground swollen stems and hypocotyls, storage roots (tap root, lateral roots, root tubers), and bulbs, that are eaten as conventional or functional food as vegetables and spices, as herbal teas, and may provide a source of food addi…
- Edition
- 1
- ISBN/ISSN
- 978-3-319-26064-8
- Collation
- -
- Series Title
- -
- Call Number
- X, 690

Advanced Computing and Systems for Security: Volume 1
The book contains the extended version of the works that have been presented and discussed in the Second International Doctoral Symposium on Applied Computation and Security Systems (ACSS 2015) held during May 23-25, 2015 in Kolkata, India. The symposium has been jointly organized by the AGH University of Science & Technology, Cracow, Poland; Ca’ Foscari University, Venice, Italy and Universi…
- Edition
- Ed. 1
- ISBN/ISSN
- 978-81-322-2650-5
- Collation
- X, 278
- Series Title
- Advances in Intelligent Systems and Computing
- Call Number
- 006.3 ADV a
Edible Medicinal and Non-Medicinal Plants
This book covers such plants with edible modified storage subterranean stems (corms, rhizomes, stem tubers) and unmodified subterranean stem stolons, above ground swollen stems and hypocotyls, storage roots (tap root, lateral roots, root tubers), and bulbs, that are eaten as conventional or functional food as vegetables and spices, as herbal teas, and may provide a source of food additive o…
- Edition
- 1
- ISBN/ISSN
- 978-3-319-26061-7
- Collation
- -
- Series Title
- -
- Call Number
- X, 392

Advanced Computing and Communication Technologies: Proceedings of the 9th ICA…
This book highlights a collection of high-quality peer-reviewed research papers presented at the Ninth International Conference on Advanced Computing & Communication Technologies (ICACCT-2015) held at Asia Pacific Institute of Information Technology, Panipat, India during 27–29 November 2015. The book discusses a wide variety of industrial, engineering and scientific applications of the emerg…
- Edition
- Ed. 1
- ISBN/ISSN
- 978-981-10-1023-1
- Collation
- XXI, 595
- Series Title
- Advances in Intelligent Systems and Computing
- Call Number
- 006.3 ADV a
Edible Medicinal and Non Medicinal Plants
Volume 9 is part of a multicompendium Edible Medicinal and Non-Medicinal Plants, on plants with edible modified stems, roots and bulbs from Acanthaceae to Zygophyllaceae (tabular) and 32 selected species in Alismataceae, Amaryllidaceae, Apiaceae, Araceae, Araliaceae, Asparagaceae, Asteraceae, Basellaceae, Brassicaceae and Campanulaceae in detail. This work is of significant interest to medical …
- Edition
- 1
- ISBN/ISSN
- 978-94-017-9510-4
- Collation
- -
- Series Title
- 73 b/w illustrations, 49 illustrations in colour
- Call Number
- X, 1036

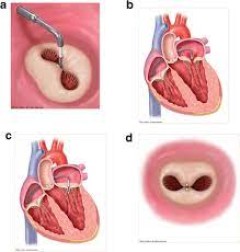
Edge-to-Edge Mitral Repair
This is the first comprehensive review of the edge-to-edge technique for mitral repair, which was introduced into the surgical armamentarium in 1991 by one of the authors, Ottavio Alfieri. The surgical technique employed in edge-to-edge repair today provides the basis for the only reliable method of percutaneous correction of degenerative mitral regurgitation. The book traces the evolution of t…
- Edition
- 1
- ISBN/ISSN
- 978-3-319-19892-7
- Collation
- -
- Series Title
- 28 b/w illustrations, 66 illustrations in colour
- Call Number
- VIII, 166
Ed.D. Programs as Incubators for Social Justice Leadership
This book shares the thoughts of mostly North American scholars on many interrelated topics that have not previously been linked in academic research. The focus of the book is the belief that the Ed.D. can prepare highly competent justice-oriented scholars who will be engaged with communities. Among these future leaders, the contributors envision educators who not only lead public schools, but …
- Edition
- 1
- ISBN/ISSN
- 978-94-6300-396-4
- Collation
- -
- Series Title
- -
- Call Number
- VIII, 206

Advanced Computer and Communication Engineering Technology: Proceedings of IC…
This book covers diverse aspects of advanced computer and communication engineering, focusing specifically on industrial and manufacturing theory and applications of electronics, communications, computing and information technology. Experts in research, industry, and academia present the latest developments in technology, describe applications involving cutting-edge communication and computer s…
- Edition
- Ed. 1
- ISBN/ISSN
- 978-3-319-24584-3
- Collation
- XV, 1325
- Series Title
- Lecture Notes in Electrical Engineering
- Call Number
- 006.3 ADV a
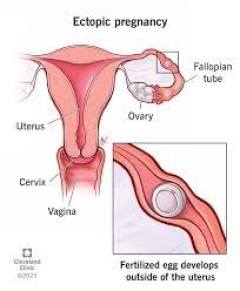
Ectopic Pregnancy
Comprised exclusively of clinical cases covering ectopic pregnancy, this concise, practical casebook will provide clinicians in reproductive medicine and obstetrics/gynecology with the best real-world strategies to properly diagnose and treat the various forms of the condition they may encounter. Each chapter is a case that opens with a unique clinical presentation, followed by a description of…
- Edition
- 1
- ISBN/ISSN
- 978-3-319-11139-1
- Collation
- -
- Series Title
- 4 b/w illustrations, 29 illustrations in colour
- Call Number
- XIV, 165
Tunable Security for Deployable Data Outsourcing
Security mechanisms like encryption negatively affect other software quality characteristics like efficiency. To cope with such trade-offs, it is preferable to build approaches that allow to tune the trade-offs after the implementation and design phase. This book introduces a methodology that can be used to build such tunable approaches. The book shows how the proposed methodology can be applie…
- Edition
- -
- ISBN/ISSN
- 978-3-7315-0411-5
- Collation
- -
- Series Title
- -
- Call Number
- 005 KOH t
 Computer Science, Information & General Works
Computer Science, Information & General Works  Philosophy & Psychology
Philosophy & Psychology  Religion
Religion  Social Sciences
Social Sciences  Language
Language  Pure Science
Pure Science  Applied Sciences
Applied Sciences  Art & Recreation
Art & Recreation  Literature
Literature  History & Geography
History & Geography